Digital Signatures of running process is needed when your want to validate that the softwares actually comes from trusted source and is unmodified by viruses or trojans. You can also check the the executable files (.exe, .dll etc,.) on your system that they are digitally signed. In Microsoft Article, it is stated that:
“Software that is downloaded from the Internet to users’ computers can contain programs such as viruses and Trojan horses that are designed to cause malicious damage or provide clandestine network access to intruders. As networks become more interconnected, malicious software and viruses also become a threat to intranets. To help counter this growing threat, you can digitally sign the software that you distribute on your intranets or the Internet to ensure its integrity and to assure others that the software can be trusted. Signed software ensures that users can verify the origin of the software, as well as verify that no one has tampered with it.
Microsoft developed the Microsoft® Authenticode® technology, which enables developers to digitally sign software. The last thing developers do before they release software is digitally sign the software. Any modification to the software after it is signed invalidates the digital signature. By using Authenticode technology, code signers who own valid X.509 version 3 code-signing certificates can sign software with their private key. Several other third-party code signing technologies also use digital certificates to enable code signing.”
Let’s see how we can check the digital signatures of files on our system if the critical windows files has been changed. We will also check the digital signature of running processes on our computer. For single file, the easiest way is right-click the file and find the Digital Signature Tab on properties. But, it is not a easy task for multiple files. So, we can say there are generally 3 methods and each has pros and cons and different features.
Method-1: Using windows built-in Signature Verification Program (sigverif.exe)
Method-2: Using SigCheck from Windows System Internals (or any third-party tools)
Method-3: Using Powershell Method
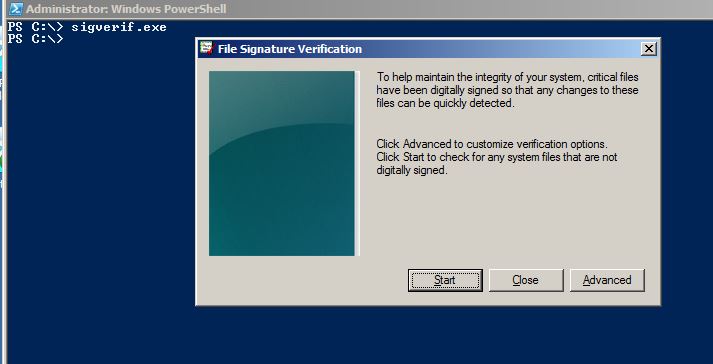
Method-1: Using windows built-in Signature Verification Program
The windows by-default included the signature verfication program to ensure that the critical system drivers has not been changed. To do this, simply type sigverif.exe in your command prompt.
sigverif.exe
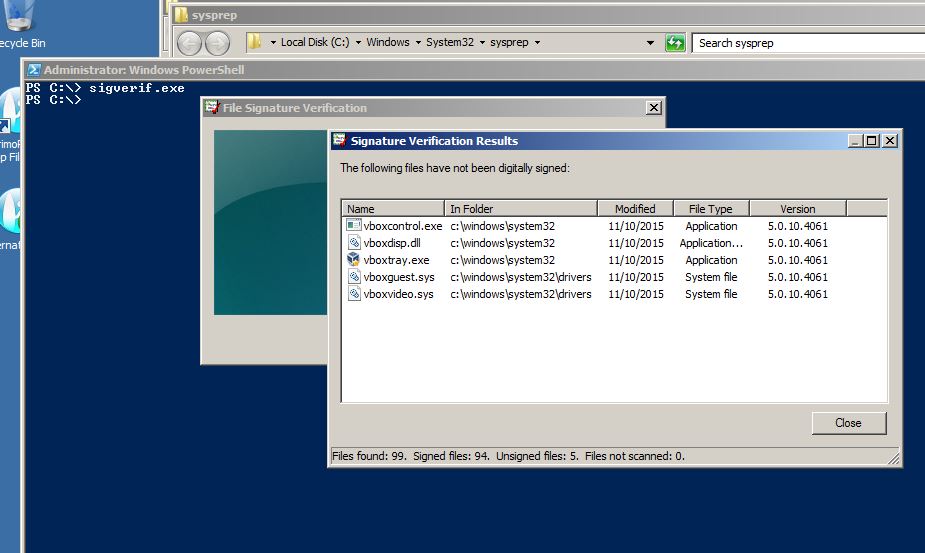
If the scan is finished, it will show up a bunch of files whose digital signatures are not signed by Microsoft (here is the oracle). See Fig-2.
Method-2: Using SigCheck from Windows System Internals
You must use this method when you use on Windows7 or server 2008R2 or earlier version where Powershell Method doesn’t work. This is because Get-AuthenticodeSignature cannot pull the signatures of some files that use digital signature that are not embedded in the content of the executable files (windows PE files) itself. These hashes of these files are stored in the security catalog files respectively which is then digitally signed again. Check Didier Stevens’s blog for details.
Download SigCheck from here, a command-line utility tools from Windows System Internals to check digital signature of files.
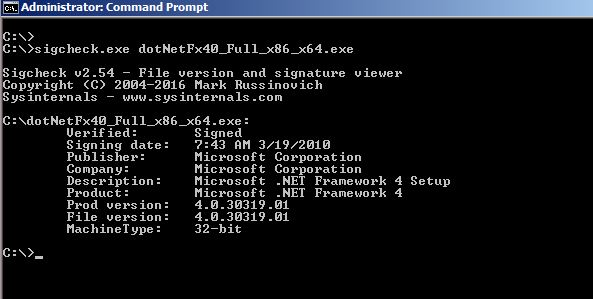
Use the command to find the digital signature of particular file. Here is how I find the digital signature of the .Net Framework 4.0 file. See Fig-3.
.sigcheck.exe <NameofFile>
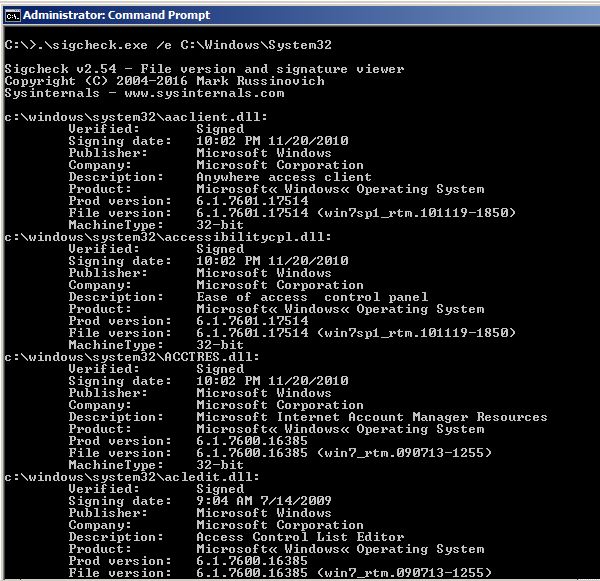
If you want to check the digital signature of all executable files under C:windowssystem32 directory, use the following command. See Fig-4.
.sigcheck.exe /e C:WindowsSystem32
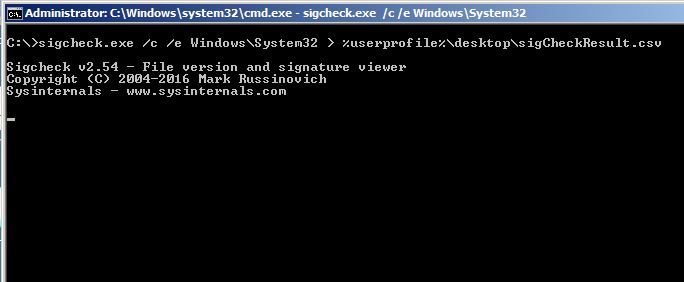
If you want to check the digital signature of all executable files under C:windowssystem32 directory and export the result to your desktop as csv file, use the following command. See Fig-5.
.\sigcheck.exe /c /e C:WindowsSystem32 > %userprofile%DesktopSigCheckResult.csv
You can get help about parameters with this command.
.\sigcheck.exe /?
Method-3: Using Powershell Method
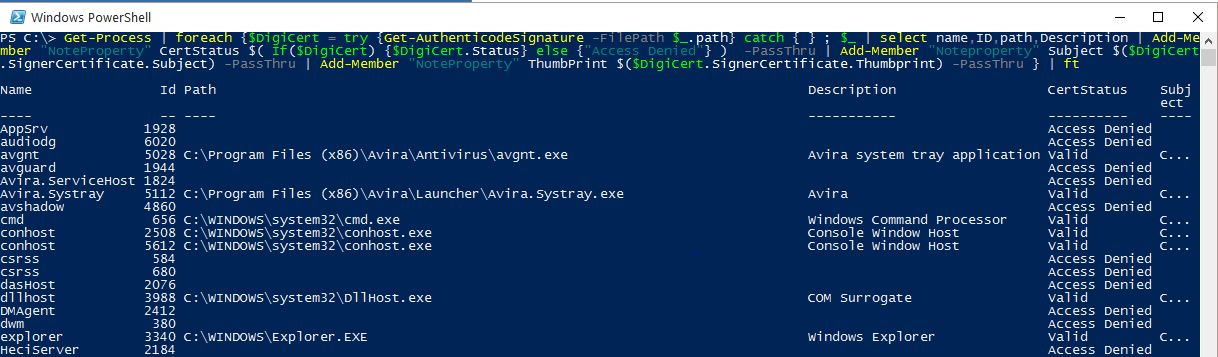
Here Get-AuthenticodeSignature is used to check the digital signature. I combined it with Get-Process to get our required output. Open powershell in adminstrative mode.
The following command will find the digital signature of all running processes. See Fig-6.
Get-Process | foreach {$DigiCert = try {Get-AuthenticodeSignature -FilePath $_.path} catch { } ; $_ | select name,ID,path,Description | Add-Member “NoteProperty” CertStatus $( If($DigiCert) {$DigiCert.Status} else {“Access Denied”} ) -PassThru | Add-Member “Noteproperty” Subject $($DigiCert.SignerCertificate.Subject) -PassThru | Add-Member “NoteProperty” ThumbPrint $($DigiCert.SignerCertificate.Thumbprint) -PassThru } | ft
If you want to output that result to csv file to your desktop, use | Export-Csv -NotypeInformation <filename>.
Get-Process | foreach {$DigiCert = try {Get-AuthenticodeSignature -FilePath $_.path} catch { } ; $_ | select name,ID,path,Description | Add-Member “NoteProperty” CertStatus $( If($DigiCert) {$DigiCert.Status} else {“Access Denied”} ) -PassThru | Add-Member “Noteproperty” Subject $($DigiCert.SignerCertificate.Subject) -PassThru | Add-Member “NoteProperty” ThumbPrint $($DigiCert.SignerCertificate.Thumbprint) -PassThru } | Export-Csv -NoTypeInformation “$env:userprofiledesktopDigitally_Signed_Files.csv”
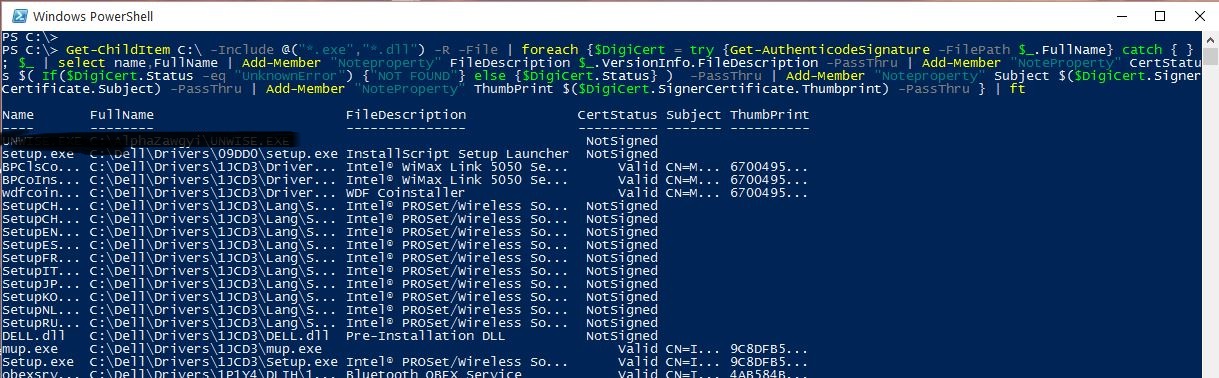
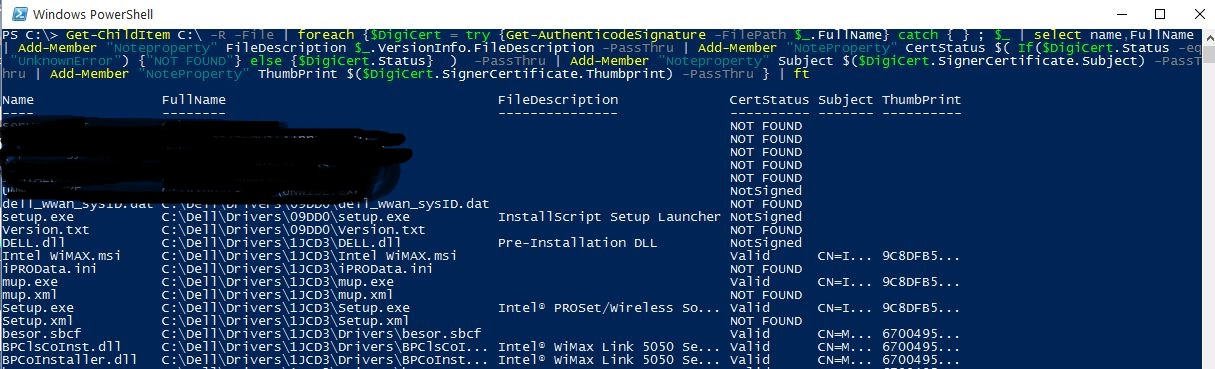
If you want to find the digital signature of all files under C: drive, use the following command. See Fig-7.
Get-ChildItem C: -R -File | foreach {$DigiCert = try {Get-AuthenticodeSignature -FilePath $_.FullName} catch { } ; $_ | select name,FullName | Add-Member “Noteproperty” FileDescription $_.VersionInfo.FileDescription -PassThru | Add-Member “NoteProperty” CertStatus $( If($DigiCert.Status -eq “UnknownError”) {“NOT FOUND”} else {$DigiCert.Status} ) -PassThru | Add-Member “Noteproperty” Subject $($DigiCert.SignerCertificate.Subject) -PassThru | Add-Member “NoteProperty” ThumbPrint $($DigiCert.SignerCertificate.Thumbprint) -PassThru } | ft
If you want to output that result to csv file to your desktop, use | Export-Csv -NotypeInformation <filename>.
Get-ChildItem C: -R -File | foreach {$DigiCert = try {Get-AuthenticodeSignature -FilePath $_.FullName} catch { } ; $_ | select name,FullName | Add-Member “Noteproperty” FileDescription $_.VersionInfo.FileDescription -PassThru | Add-Member “NoteProperty” CertStatus $( If($DigiCert.Status -eq “UnknownError”) {“NOT FOUND”} else {$DigiCert.Status} ) -PassThru | Add-Member “Noteproperty” Subject $($DigiCert.SignerCertificate.Subject) -PassThru | Add-Member “NoteProperty” ThumbPrint $($DigiCert.SignerCertificate.Thumbprint) -PassThru } | Export-Csv -NoTypeInformation “$env:userprofiledesktopDigitally_Signed_Files.csv”
You can only include only .exe and .dll files, use the following command. See Fig-8.
Get-ChildItem C: -Include @(“*.exe”,”*.dll”) -R -File | foreach {$DigiCert = try {Get-AuthenticodeSignature -FilePath $_.FullName} catch { } ; $_ | select name,FullName | Add-Member “Noteproperty” FileDescription $_.VersionInfo.FileDescription -PassThru | Add-Member “NoteProperty” CertStatus $( If($DigiCert.Status -eq “UnknownError”) {“NOT FOUND”} else {$DigiCert.Status} ) -PassThru | Add-Member “Noteproperty” Subject $($DigiCert.SignerCertificate.Subject) -PassThru | Add-Member “NoteProperty” ThumbPrint $($DigiCert.SignerCertificate.Thumbprint) -PassThru } | ft