Hi fellow scripters, I’m pretty sure this handy script will help system admins to make a day-to-day AD operation super easy. You can quickly jump into the screenshots to get an overview idea. Note that Powershell module for AD is required for this script.
Things to note:
By running this script, all users/groups in the text file or all child users/groups under the defined OU will be affected. So, make sure you are completely aware of the explanation of parameters you want to do with the script. The suggestion is to test on your non-production systems first.
Here is what you can expect from the script:
- Extract the AD user attributes (single attributes or bulk attributes)
- Extract users based on the bulk AD groups
- Extract associated AD groups membership based on bulk users
- Add or Remove bulk users to the specified group
- Enable or Disable bulk users
- Delete bulk AD users
- Reset Password Timestamp of bulk users (usually done to avoid the password change when the user password expires)
- Reset bulk users password
- Set bulk users account expiry date
Here is the complete list of parameters:
-TxtFilePath : The text file where user or group names are separated line-by-line. The selected operations (-Operation) will be performed on these users or groups. You should use sAMAccountName the for the users and the group. And users and groups cannot exist in the same file.
-OUDistinguishedName : The distinguished name of the OU under which all child users or groups will be used for further processing (the purpose is same as the -TxtFilePath).
-GroupName : The group name which will be used for group membership add or remove operations against the users specified.
-PasswordString : The password string which will be used for the password reset operation (when you use -Operation ResetPassword)
-AccountExpiryDate : The datestamp which will be used to set the account expiry date. Value should be given as MM/dd/yyyy format
-Operation : The AD operation that you want to perform on users or groups which are defined in the Txt file or OU path. Use one of the following available operations:
- GetUsersAttribute : Get the required attributes of the users (defined in Text file or as OU DistinguishedName) and save to the csv file. Please note that you have to enter the attribute names (as you see in the Attribute Editor Tab of dsa.msc) and press Enter
- GetUsersFromGroups : Get all users from the specific groups (defined in Text file or as OU DistinguishedName) and save the result to the ‘Members Of .txt’ file. You need to use the -TxtFilePath or -OUDistinguishedName
- GetGroupsFromUsers : Get the groups of the users (defined in Text file or as OU DistinguishedName), and separated by commas and save into the file ‘AD_Users_and_Groups_Info.csv’
- AddUsersToGroup : Add users (defined in Text file or as OU DistinguishedName) into the specific group (defined as -GroupName)
- RemoveUsersFromGroup : Remove users (defined in Text file or as OU DistinguishedName) from the specific group (defined as -GroupName)
- EnableUsers : Enable users (defined in Text file or as OU DistinguishedName)
- DisableUsers : Disable users (defined in Text file or as OU DistinguishedName)
- DeleteUsers : Delete users (defined in Text file or as OU DistinguishedName)
- ResetPasswordTimeStamp : Reset the password timestamp of users (so that users password expiration is extended for a next period eg: 3 months as defined by AD policy)
- ResetPassword : Reset users’ password. You need to defind the password string with -PasswordString in quotes.
- SetAccountExpiryDate : Set the account expiry date of user accounts. The date should be given as MM/dd/yyyy.
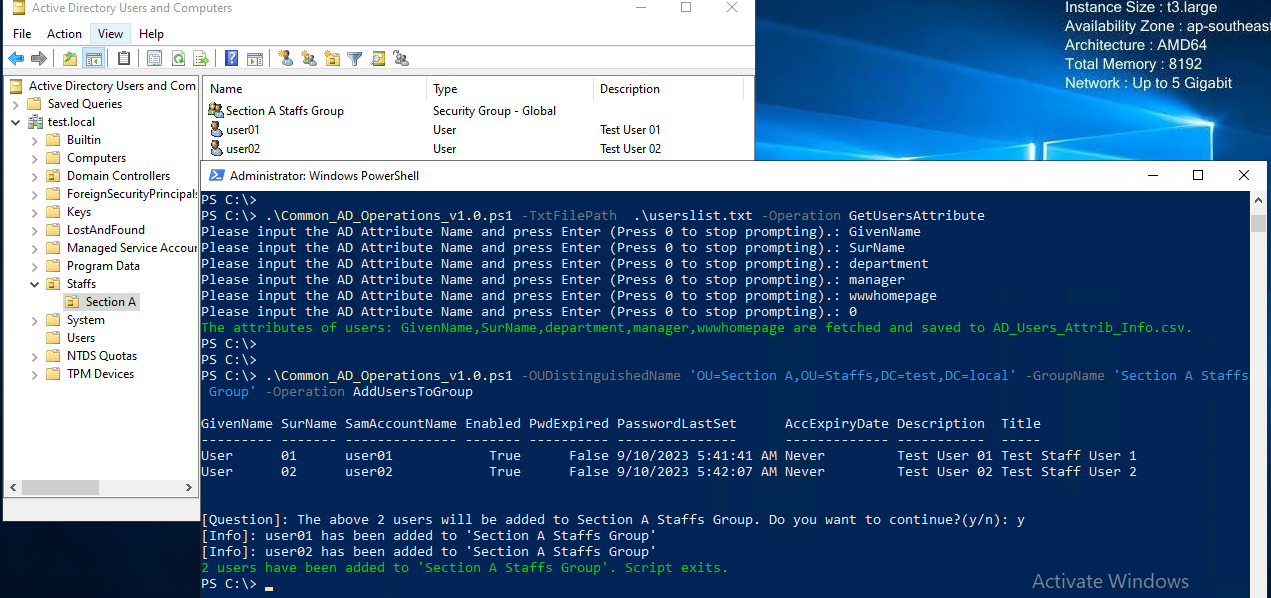
Fig-1: Extract user attributes and add users to specific group
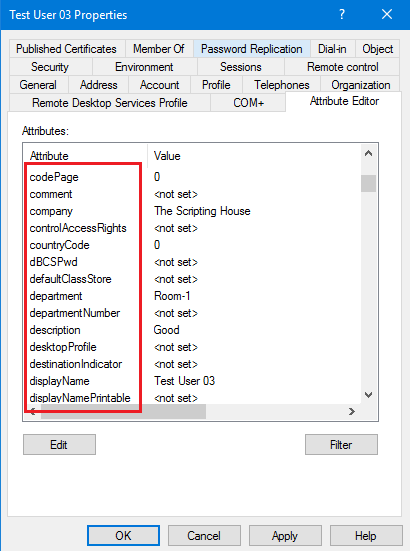
Fig-2: You can use any of attribute names in the attribute editor tabs to get user attributes
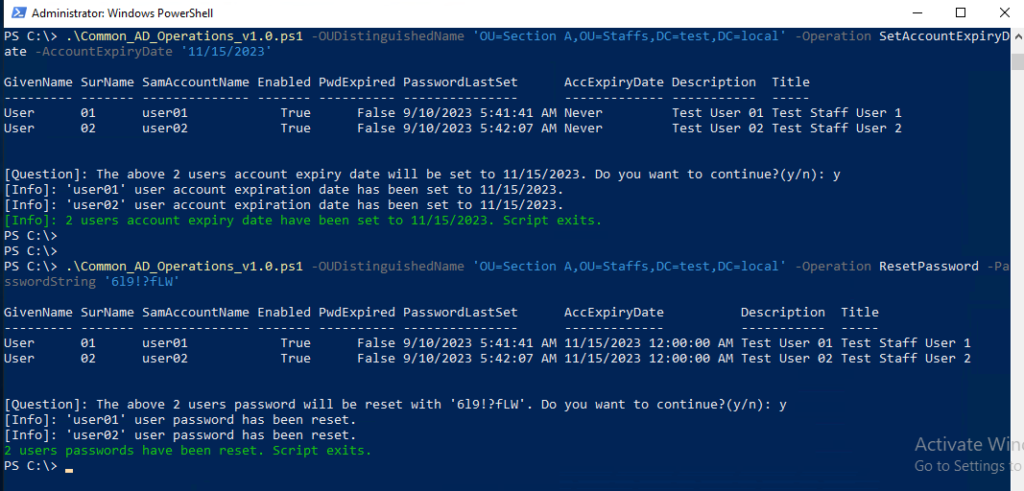
Fig-3: Set Account Expiry and Reset Users Passwords
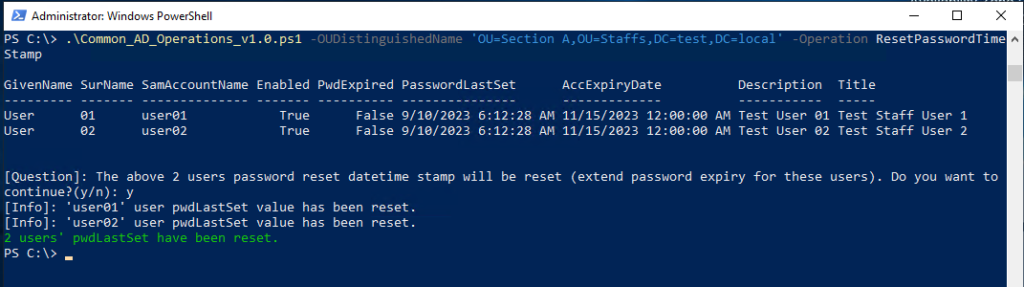
Fig-4: Reset Password Expiry Timestamp
You can download the below script from my gist.