Go to >> Part-1:Install ADCS service and configure Code Signing Certificate Template
Go to >> Part-2: Request the certificate to sign the script by user1
Go to >> Part-3: Configure GPO to allow only signed scripts and add user1’s certificate to trusted publisher group on domain computers
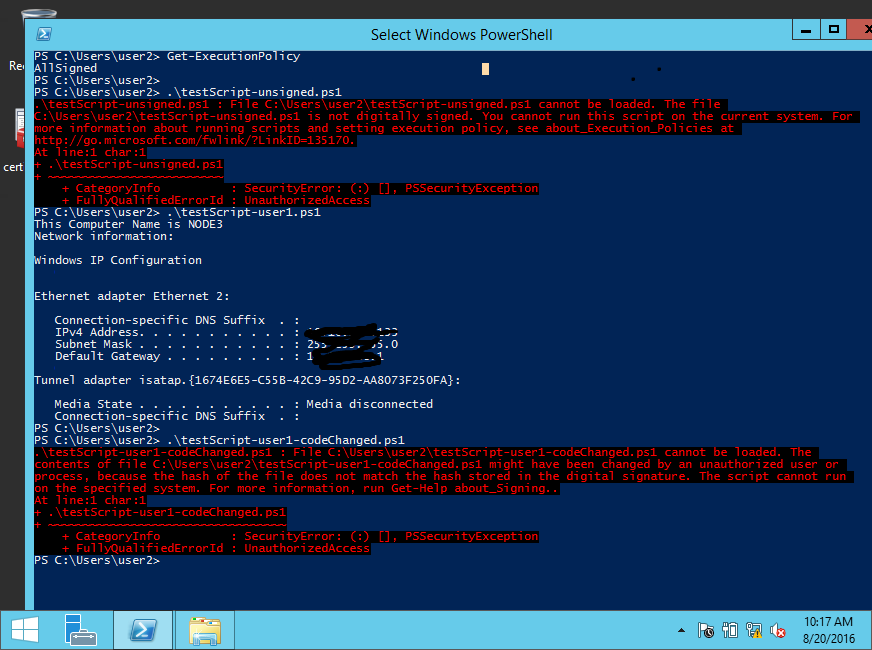
Now, it’s time to test running the script. Let’s say user2 has recently joined to your company and try to run some script downloaded from internet on Node-2 computer which is a newly domain joined computer. Also, don’t forget to “gpupdate” on client computers after your GPO is changed.
Here, we will do the following test cases:
Test case-1: user2 run unsigned script on computer Node-2.
Result: user2 cannot run the unsigned script because Node-2 computer is enforced by GPO not to run any unsigned scripts.
Test case-2: user2 gets the script written and signed by user1 and tries to run on Node-2 computer.
Result: user2 can run the script successfully since the script is digitally signed and unmodified.
Test case-3: user2 changes some code of user1’s script and tries to run on Node-2 computer.
Result: user2 cannot run the script because the digital signature of certificate does not match the hash value of the file, which content has been changed.
You can see the output in Figure-1.
Note: I used the same command windows for various tests.