Unlike a normal FTP server, the magic of FTP with user isolation is that every user
is jailed in this own directory and the user cannot see or write to other users’ directories, as well as changing to the parent root directory. In linux, it is similar to “chroot” option after the user has logged into his home directory.
Today, I will show you how to make ftp with user isolation in IIS 8.5 (also tested on server 2008R2 with IIS 7.5) with Domain user accounts in graphical Mode. Also, I have made a good powershell script to automate this ftp setup process for thousand of users ;P. Continue reading “The Magic of FTP with user isolation and how to automate the setup with Powershell (with Domain Users)”
Year: 2016
IIS Worker Process (w3wp.exe) memory usage too high in Exchange Server
w3wp.exe process is an IIS web application process to handle the client request for the application pool. Exchange server services heavily utilized w3wp process not only to handle users request from external but themselves make web service requests among Exchange server members using virtual directories (Owa, OAB & Powershell etc) and respective App pools. Unless you have not configured periodic recycling for Application Pool, you may need to do manual recycle to avoid memory leaks. Microsoft Technet states that: Continue reading “IIS Worker Process (w3wp.exe) memory usage too high in Exchange Server”
Powershell: Find AD Users’ Logon History with their Logged on Computers
One of the daily system admin task is to check the user login history throughout the domain. It becomes quite a tough task if you have to go through thousands of event logs to find the correct security events of users logon from every domain controllers. Though we filter only the Kerberos Authentication Events for TGT (Ticket-Granting-Ticket) Requests, there are so many information in each event regarding to specific users.
So, I am taking some time to put all these Kerberos events together from every domain controller to look for some useful information and then write this handy script to save my difficult days ! Continue reading “Powershell: Find AD Users’ Logon History with their Logged on Computers”
How to Digitally Sign the Powershell Scripts with Microsoft CA in Domain – A step-by-step Guide – Part 4
Go to >> Part-1:Install ADCS service and configure Code Signing Certificate Template
Go to >> Part-2: Request the certificate to sign the script by user1
Go to >> Part-3: Configure GPO to allow only signed scripts and add user1’s certificate to trusted publisher group on domain computers
Now, it’s time to test running the script. Let’s say user2 has recently joined to your company and try to run some script downloaded from internet on Node-2 computer which is a newly domain joined computer. Also, don’t forget to “gpupdate” on client computers after your GPO is changed. Continue reading “How to Digitally Sign the Powershell Scripts with Microsoft CA in Domain – A step-by-step Guide – Part 4”
How to Digitally Sign the Powershell Scripts with Microsoft CA in Domain – A step-by-step Guide – Part 3
3) Configure GPO to allow only signed scripts and add user1’s certificate to trusted publisher group on domain computers
Go to >> Part-1:Install ADCS service and configure Code Signing Certificate Template
Go to >> Part-2: Request the certificate to sign the script by user1
Go to >> Part-4: Run the test scripts
In Part-2, we have signed the script with user1’s certificate. There are some manual works such as adding user1 certificate to trusted publisher group. Let us see how can we automate this process by using GPO.
First of all, we need to export user1 certificate from Node1 computer’s personal store to DC1 computer where we can distribute this certificate via Group Policy. Continue reading “How to Digitally Sign the Powershell Scripts with Microsoft CA in Domain – A step-by-step Guide – Part 3”
How to Digitally Sign the Powershell Scripts with Microsoft CA in Domain – A step-by-step Guide – Part 2
2) Request the certificate the sign the script by user1
Go to >> Part-1:Install ADCS service and configure Code Signing Certificate Template
Go to >> Part-3: Configure GPO to allow only signed scripts and add user1’s certificate to trusted publisher group on domain computers
Go to >> Part-4: Run the test scripts
In the Part-1, we have configured AD CS role and configure certificate template. Now, it’s time that user1 request his certificate and sign his script. On the Node-1 computer with user1 logged on as domain user: Continue reading “How to Digitally Sign the Powershell Scripts with Microsoft CA in Domain – A step-by-step Guide – Part 2”
How to Digitally Sign the Powershell Scripts with Microsoft CA in Domain – A step-by-step Guide – Part 1
Go to >> Part-2: Request the certificate the sign the script by user1
Go to >> Part-3: Configure GPO to allow only signed scripts and add user1’s certificate to trusted publisher group on domain computers
Go to >> Part-4: Run the test scripts
This is a lengthy post of how to digitally sign your powershell script, so I divide it up to 4 sections. Digitally signing of powershell script, for the security purpose, is particularly useful to prevent the execution of malicious scripts on servers or workstations in your domain environment. Today, I will show you how to sign your powershell scripts from Microsoft CA and use GPO to control the execution of unsigned scripts in domain environment. Continue reading “How to Digitally Sign the Powershell Scripts with Microsoft CA in Domain – A step-by-step Guide – Part 1”
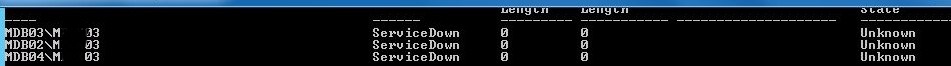
Recover Crashed Exchange 2013 Mailbox Server in DAG
-
Reset the crashed computer accounts in AD.
-
Install new server OS to replace the old crashed servers. Install windows features, pre-requisites and updates.
-
Remove the database passive copies on crashed servers. If the servers are accessible you can manually delete DB file and logs file residues from crashed servers.
-
Remove the crash servers from DAG. This can be done by EMC or EMS.
-
Evict(remove) the crash servers from failover cluster manager.
-
Start the recovery process by running setup file in command prompt with necessary switches. More details later in this section.
Install-WindowsFeature AS-HTTP-Activation, Desktop-Experience, NET-Framework-45-Features, RPC-over-HTTP-proxy, RSAT-Clustering, RSAT-Clustering-CmdInterface, Web-Mgmt-Console, WAS-Process-Model, Web-Asp-Net45, Web-Basic-Auth, Web-Client-Auth, Web-Digest-Auth, Web-Dir-Browsing, Web-Dyn-Compression, Web-Http-Errors, Web-Http-Logging, Web-Http-Redirect, Web-Http-Tracing, Web-ISAPI-Ext, Web-ISAPI-Filter, Web-Lgcy-Mgmt-Console, Web-Metabase, Web-Mgmt-Console, Web-Mgmt-Service, Web-Net-Ext45, Web-Request-Monitor, Web-Server, Web-Stat-Compression, Web-Static-Content, Web-Windows-Auth, Web-WMI, Windows-Identity-Foundationsetup.exe /m:RecoverServer /IAcceptExchangeServerLicenseTerms
You can also check your current exchange server version with build numbers on good servers in EMS shell by:
[PS] C:\>Get-ExchangeServer | Format-List Name, Edition, AdminDisplayVersion
As the recovery process is fetching info from AD objects and reinstalling the exchange server, you can see the progress in the console.
Search Multiple Words in Multiple Excel files using Powershell !
Inventory documentation with Excel is something that most infrastructure administrators have to deal with on a daily basis. Sometimes, I have to search for a bulk of IP addresses in multiple Excel files, but I have to do it by opening the Excel files one by one. After investigating how this can be achieved in PowerShell, I found that using comObject is the way to go, as it can be used to automate most Windows applications. Make sure Microsoft Excel is already installed before you run the script.
How to use the script:
You need to create search values.txt file and insert the contents line-by-line that you want to search. (Also the script will automatically create the search values.txt on the first run if not exists). The output files will have the same names as original files appended with _RESULT.xlsx
Then, open powershell console and run with following necessary parameters. You will need to specify -Folder or -File parameter at least.
Example:
.\Excel_search.ps1 C:\MyExcelFiles -Recurse -Color -OpenFile -Grid
Parameters:
-Folder : The folder name in which multiple Microsoft Excel files should already exist (Use it if the -File is not specified)
-File : The file name of the Microsoft Excel file (Use it if the -Folder is not specified)
-Recurse : Use this with -Folder option to search excel files recursively
-Color : Use this to colorize the values found in the excel files (in darkblue color)
-Grid : Use this to display the summary of search results in grid output windows (See Fig-1)
-OpenFile : Use this to automatically open the output files when the search operation is completed.
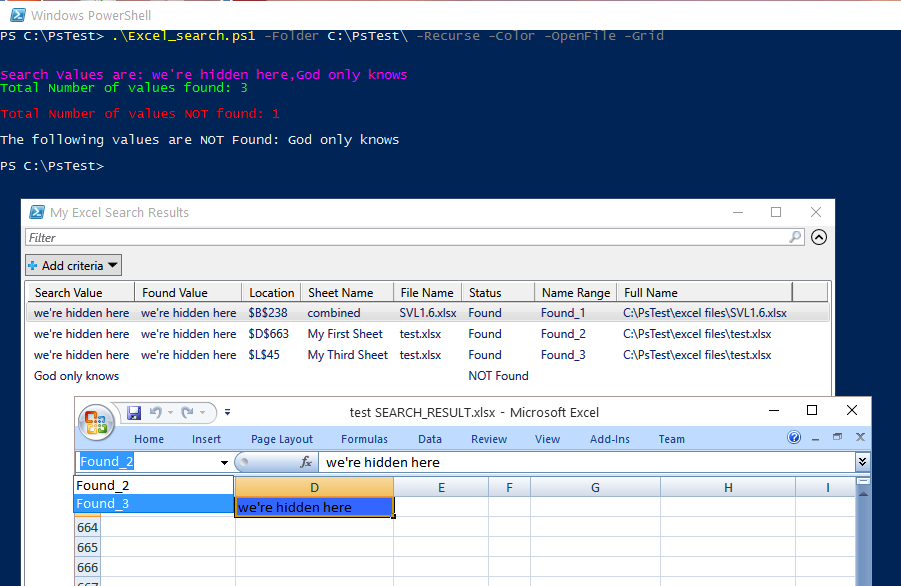
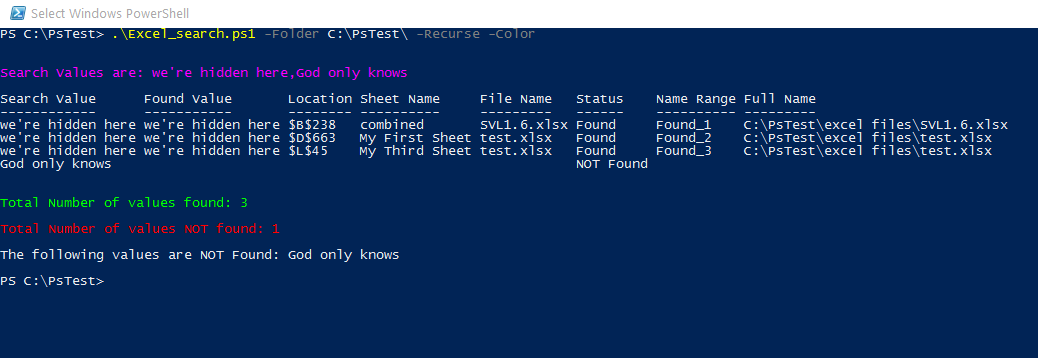
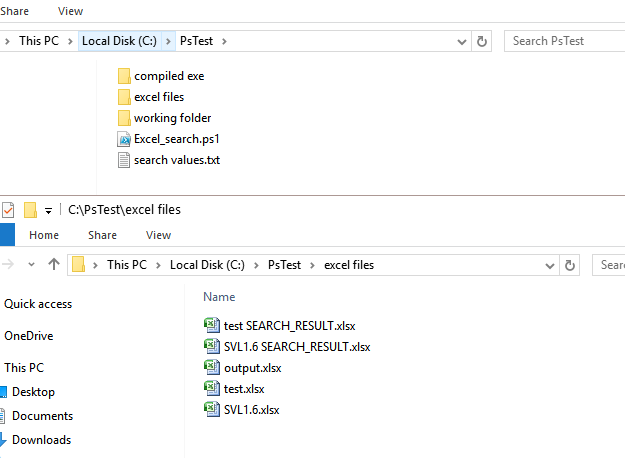
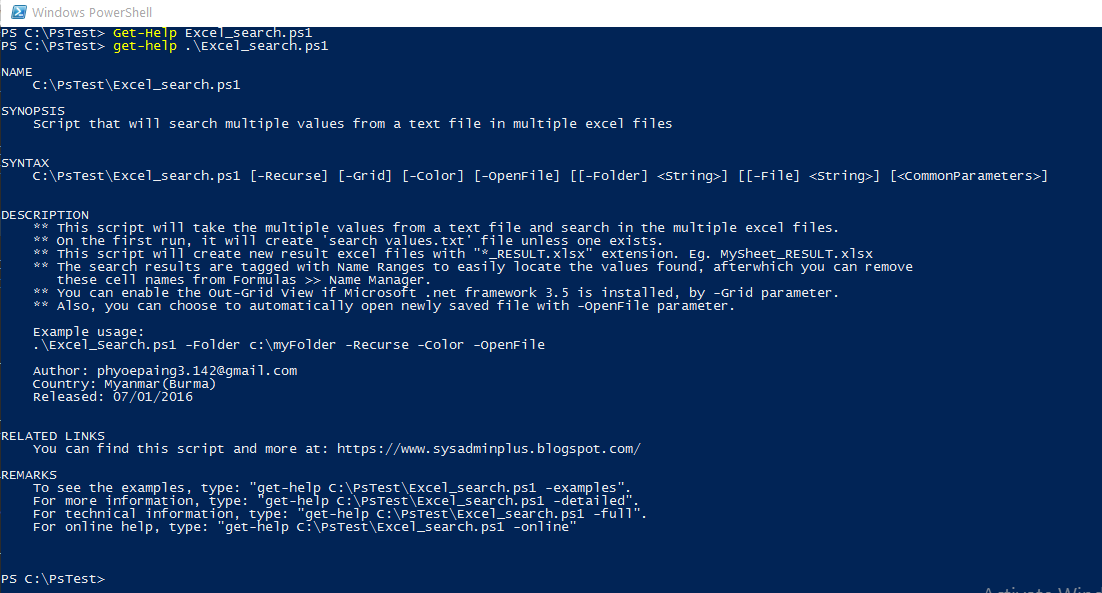
You can download my script from github.
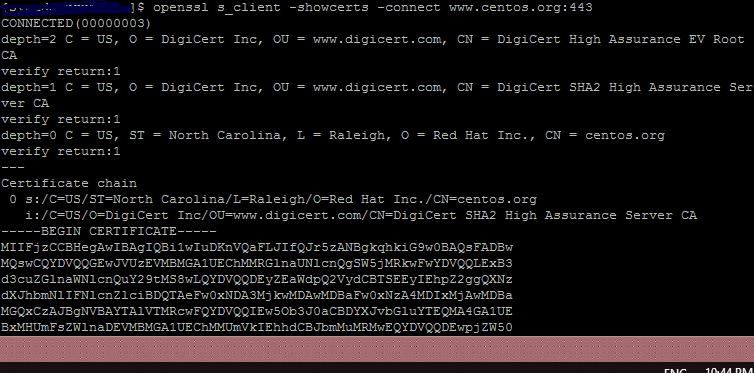
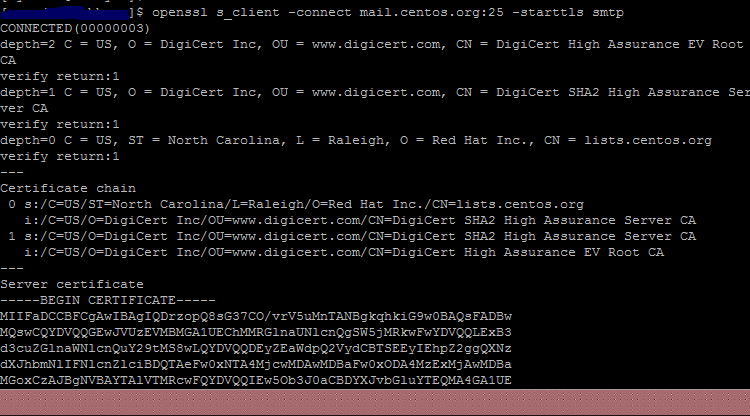
View SSL/TLS Certificate Info with OpenSSL Command
You can simply check the SSL/TLS certificate information which is listening at non-http port (like STMP) by using the OpenSSL tool. All you need to know is to the port that uses encrypted connection. For example, I view the certificate info at CentOS website & TLS certificate used for smtp connection. With WSL, OpenSSL already installed and you’re ready to go.
For example here, I check the CentOS website & TLS certificate which is used for smtp connection.
For SSL connection:
openssl s_client -showcerts -connect www.centos.org:443
For TLS connection:
openssl s_client -connect mail.centos.org:25 -starttls smtp